Examples Of Transmission Security . Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Prevents the interception or disruption of any transmissions occurring over a. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent.
from www.slideserve.com
Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Prevents the interception or disruption of any transmissions occurring over a. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,.
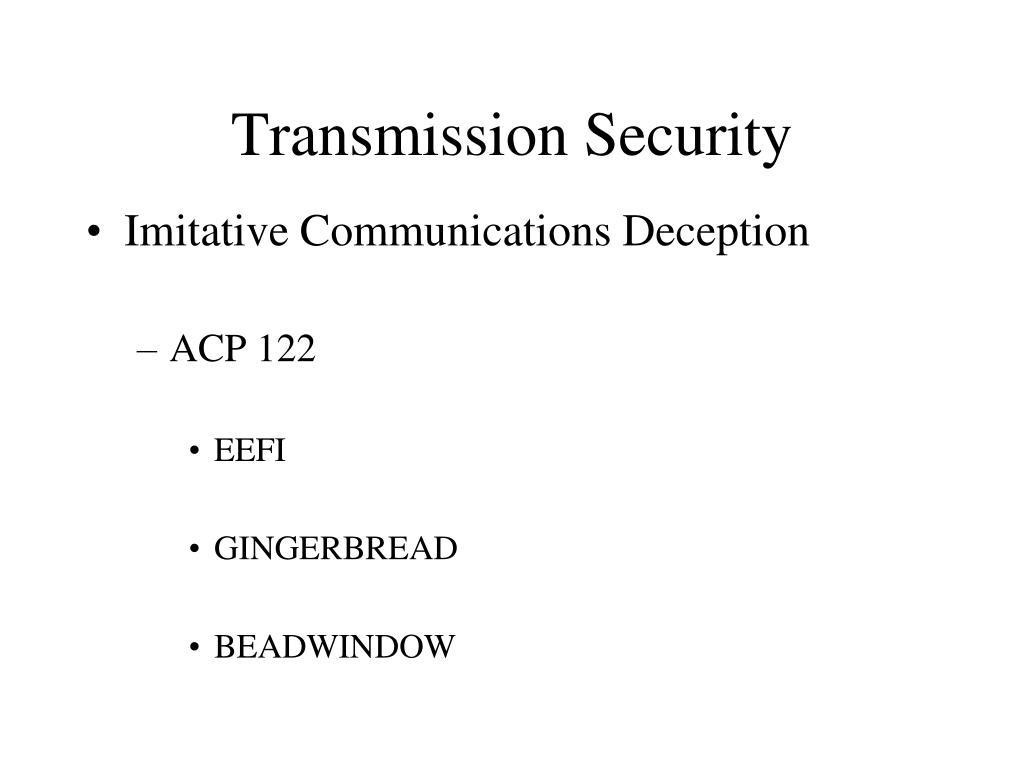
PPT Topic 6 Security Enabling Objectives PowerPoint Presentation
Examples Of Transmission Security Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Prevents the interception or disruption of any transmissions occurring over a.
From slideplayer.com
Chapter 8 Information Security. ppt download Examples Of Transmission Security Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web transmission security (transec) is the process of securing data transmissions from. Examples Of Transmission Security.
From www.alamy.com
Network data transmission and lock, dollars, security protection Stock Examples Of Transmission Security Prevents the interception or disruption of any transmissions occurring over a. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web transmission security. Examples Of Transmission Security.
From noise.getoto.net
Automatic (secure) transmission taking the pain out of origin Examples Of Transmission Security Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web threat actors readily stand by to monitor, exploit, or intercept communications for. Examples Of Transmission Security.
From www.conceptdraw.com
Network Security Tips Examples Of Transmission Security Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web threat actors readily stand by to monitor, exploit, or intercept communications for. Examples Of Transmission Security.
From www.youtube.com
Implementation Of Secure Image Transmission Technique YouTube Examples Of Transmission Security Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two. Examples Of Transmission Security.
From www.slideserve.com
PPT COMSEC Security) PowerPoint Presentation, free Examples Of Transmission Security Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Prevents the interception or disruption of any transmissions occurring over a. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web threat. Examples Of Transmission Security.
From www.educba.com
Security Architecture Components of Security Architecture Examples Of Transmission Security Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Prevents the interception or disruption of any transmissions occurring over a. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web. Examples Of Transmission Security.
From www.researchgate.net
Simple secure transmission. Download Scientific Diagram Examples Of Transmission Security Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Prevents the interception or disruption of any transmissions occurring over a. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web you can minimize. Examples Of Transmission Security.
From profentech.com
Transmission Security (TRANSEC) Technology Brief Profen Communication Examples Of Transmission Security Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Prevents the interception or disruption of any transmissions occurring over a. Web threat. Examples Of Transmission Security.
From www.slideserve.com
PPT COMSEC Security) PowerPoint Presentation, free Examples Of Transmission Security Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web you can minimize the risks associated with moving information across untrusted systems with two. Examples Of Transmission Security.
From www.researchgate.net
Secure transmission as a service examples. Download Scientific Diagram Examples Of Transmission Security Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web transmission security (transec) is the process of securing data transmissions from. Examples Of Transmission Security.
From www.slideserve.com
PPT Topic 6 Security Enabling Objectives PowerPoint Presentation Examples Of Transmission Security Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Prevents the interception or disruption of any transmissions occurring over a. Web. Examples Of Transmission Security.
From www.dreamstime.com
Secure Data Transmission Concept. Access Right. Safe File Sharing Examples Of Transmission Security Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Prevents the interception or disruption of any transmissions occurring over a. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web you can minimize. Examples Of Transmission Security.
From www.youtube.com
Unit 1 Secure Communication Transmission Security YouTube Examples Of Transmission Security Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Prevents the interception or disruption of any transmissions occurring over a. Web threat. Examples Of Transmission Security.
From www.youtube.com
Link Encryption Ensuring Secure Data Transmission Explained with Examples Of Transmission Security Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Prevents the interception or disruption of any transmissions occurring over a. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web threat. Examples Of Transmission Security.
From www.slideserve.com
PPT HIPAA Security PowerPoint Presentation, free download ID4068979 Examples Of Transmission Security Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols. Examples Of Transmission Security.
From devsday.ru
Automatic (secure) transmission taking the pain out of origin Examples Of Transmission Security Web you can minimize the risks associated with moving information across untrusted systems with two specific transmission. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Prevents the interception or disruption of any transmissions occurring over a. Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web threat. Examples Of Transmission Security.
From eureka.patsnap.com
Data Transmission Security Improvements Eureka Patsnap Examples Of Transmission Security Web transmission security (transec) is the process of securing data transmissions from being infiltrated,. Web threat actors readily stand by to monitor, exploit, or intercept communications for malicious intent. Web transmission security works by enforcing security policies, use of encryption algorithms, secure protocols and other. Web you can minimize the risks associated with moving information across untrusted systems with two. Examples Of Transmission Security.